Securing Your DevOps Pipelines
- Background on DevOps
- Security in DevOps or DevSecOps
- DevSecOps Tools
- Setting up a DevSecOps Pipeline
- Final Security Checks
Background on DevOps
1.1 Understand where DevOps came from
Long development cycles lead to cascading problems
- Security issues
- Feature conflicts
- QA bottleneck
- Scope creep
- Overlapping development
Business needed to speed up deploy cycles.
- Develop -->QA Bugs-->Back to develop-->Add more features
The process needed to be reproducible.
Needed to handle a number of steps.
- Build artifact
- Run unit tests
- Report failed tests
- Set environment variables
- Deploy to QA
- Run integration tests
- Deploy to staging
- Clear cache
- Deploy to feature environment
- Deploy to production
1.2 Learn how DevOps Works
Plan
Gather all of the feature requirements.
Code
Implement the code to add the feature to the application.
Build
Create the application build files.
Test
Run unit tests, do quality assurance (QA), and run integration tests.
Release
Tag a release of the approved feature implementation.
Deploy
Ship the approved feature implementation to production.
Operate
Keep the application running for end users and customers.
Monitor
Watch for any changes in the application's functionality.
1.3 DevOps versus Waterfall
Everything needs to be finished before deploying.
Incremental release make it less likely for bugs to get to production.
Harder to make changes when feedback comes.
Allow stakeholders to test out functionality as it is completed.
Can make code changes take months to release.
Able to release code changes multiple times per day.
New code slowly gets added to the initial request.
Controls scope creep.
Security gets left until the very end.
Security can be added in a number of places.
Security in DevOps or DevSecOps
2.1 Show where security comes in
Previously at the end of the waterfall
- Feature development, QA, build candidate
- Security testing
- Deployment
Happens at each stage in the pipeline
- Feature development
- Security testing
- QA
- Security testing
Detecting issues early shortens development.
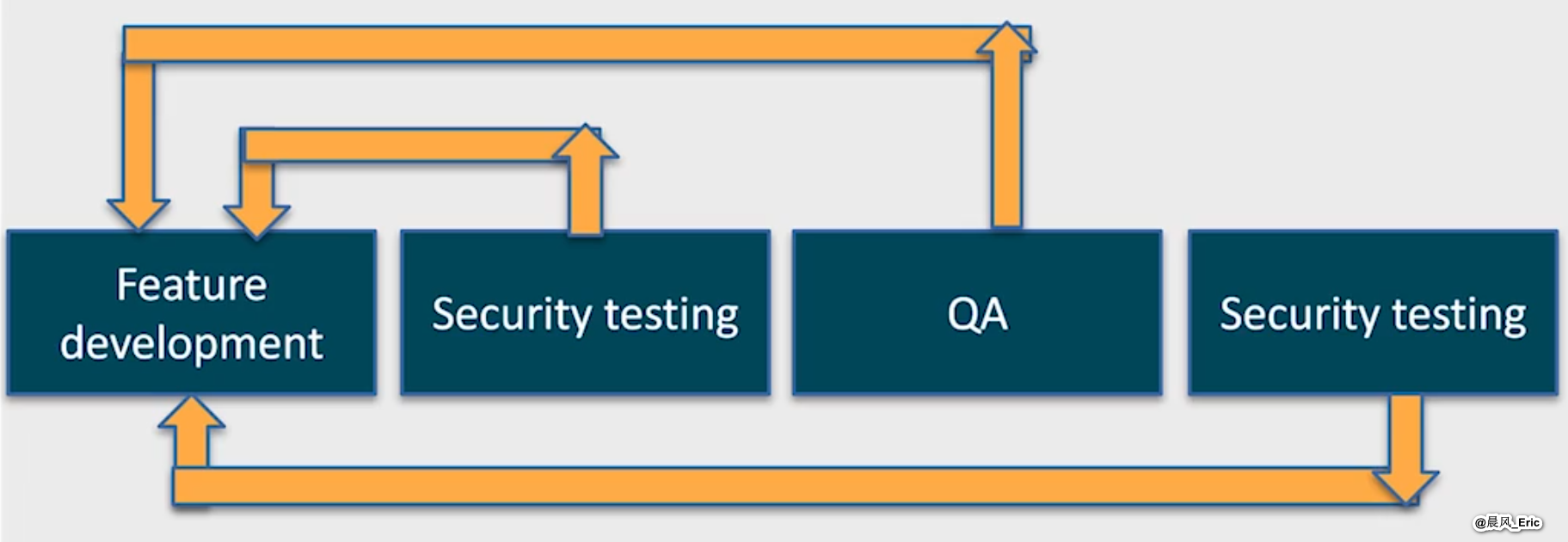
Easier to include before issues arise.
2.2 Learn how issues get to production
Time restrictions
Hard to get answers
- What stages should run in parallel?
- What are the auth methods for services?
- Which CLI tools should be used?
Unfamiliar with tools
- Google Cloud
- Docker
- AWS
- Kubernetes
- Azure
- Redis
Unfamiliar with pipelines
2.3 Learn the OWAPS 10 Top security risks
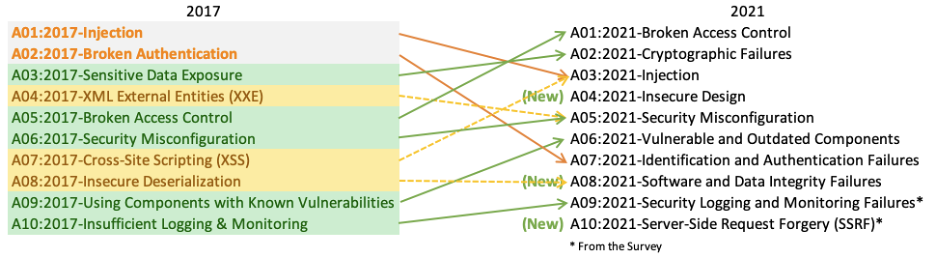
https://owasp.org/www-project-top-ten/assets/images/mapping.png
Broken Access Control
Bypass access control checks by adding parameters to the URL.
APIs with missing access controls for POST, PUT and DELETE requests
Not following the principle of least privilege.
Cryptographic Failures
Data transmitted in clear text
Use of deprecated dash functions such as MD5 or SHA1
Have crypto keys checked into source code repositories.
Injection
No validation on user input.
Malicious data gets used in SQL queries
Scripts get add to and executed on a web page
Insecure Design
Missing or ineffective control design.
Security isn't addressed in user stories.
Certain user flow logic is weak.
Security Misconfiguration
Default user names and passwords are still in place for services.
Unnecessary features are installed that open access to restricted data.
Too much information is shared with users in error messages.
Vulnerable and Outdated Components
Current versions of the libraries used are behind the newest versions.
Compatibility with different libraries goes unchecked
Libraries are installed from unreliable sources.
2.4 Understand how attackers gain unauthorized access to apps
They use a number of free and paid tools.
They check for app and system misconfigurations.
They look for secrets in your version control.
They check for extra open ports.
They look for vulnerabilities in your packages.
2.5 Learn the basics of DevSecOps access to apps
Adds automated security best practices to DevOps
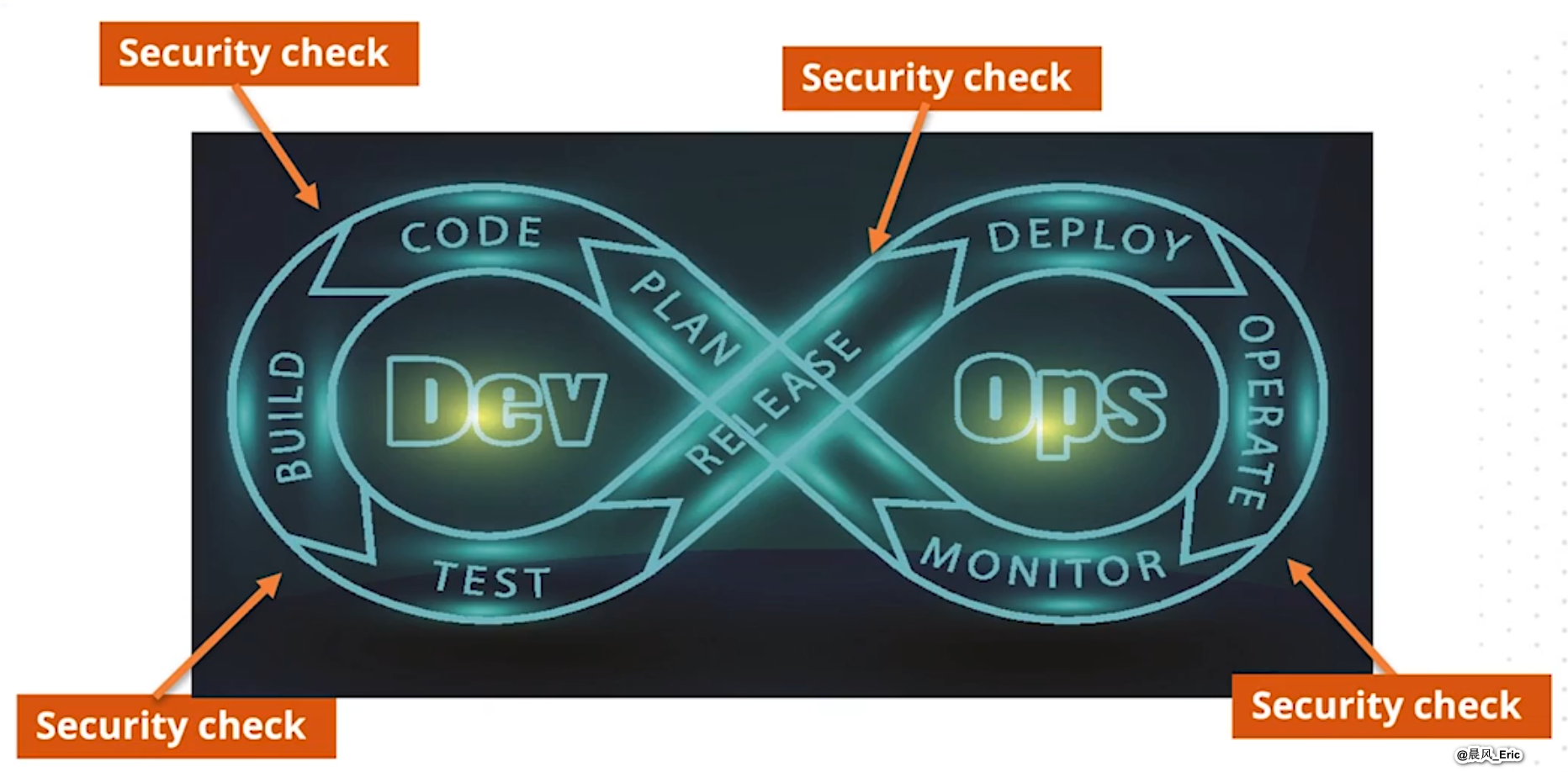
Keeps security considerations front of mind for each pipeline stage.
Spreads the responsibility of how security is addressed.

2.6 Use DevSecOps to mitigate risks
Detect common security vulnerabilities automatically.
Monitoring sends alerts to the right teams.
Get feedback faster when new risks are noted.
Lots of tools available.
DAST, OAST, SAST, IAST, Cloud security, Issue tracking
