本篇目录
- Private VLAN概述
- Private VLAN配置限制
- Private VLAN配置步骤
- 端口工作模式详解及配置
- Private VLAN配置过程示例
- 配置验证命令
1. Private VLAN概述
Private VLAN(私有VLAN)是一种二层VLAN结构,通过配置Primary和Secondary两类VLAN,在保证用户隔离的同时节省VLAN资源。Secondary VLAN间二层报文互相隔离,多个Secondary VLAN可映射到一个Primary VLAN,上行设备只需知道对应的Primary VLAN。
2. Private VLAN配置限制
- 不支持组播功能
- 不支持与VXLAN IP网关功能组合使用
- Primary VLAN和Secondary VLAN的VLAN接口MAC地址需保持一致
- 系统缺省VLAN(VLAN 1)不支持Private VLAN配置
- 配置完成后需验证各端口VLAN成员关系是否正确
3. Private VLAN配置步骤
配置上行/下行端口详见4端口工作模式详解及配置
配置 VLAN
# 进入系统视图
<H3C> system-view# 创建VLAN并进入VLAN视图
[H3C] vlan 10
# 配置VLAN类型为Primary VLAN
[H3C-vlan10] private-vlan primary
[H3C-vlan10] quit# 创建Secondary VLAN
[H3C] vlan 2 to 3
建立映射关系
# 进入Primary VLAN视图
[H3C] vlan 10# 建立Primary VLAN与Secondary VLAN的映射关系
[H3C-vlan10] private-vlan secondary 2 to 3
[H3C-vlan10] quit
配置Secondary VLAN间三层互通(可选)
/*同一Secondary VLAN内端口二层互通*/
# 进入Secondary VLAN视图
<H3C> system-view
[H3C] vlan 2# 配置为Community VLAN(社区VLAN,默认互通)
[H3C-vlan2] private-vlan community
# 取消隔离(如果之前配置了隔离)
[H3C-vlan2] undo private-vlan isolated
[H3C-vlan2] quit
# 其他Secondary VLAN同理/*Secondary VLAN间三层互通*/
# 创建Primary VLAN接口
[H3C] interface vlan-interface 10# 配置IP地址(ipv6也行)
[H3C-Vlan-interface10] ip address 192.168.1.1 255.255.255.0# 开启本地代理ARP功能(实现Secondary VLAN间三层互通)
[H3C-Vlan-interface10] local-proxy-arp enable
# 如果是ipv6对应 -> local-proxy-nd enable
[H3C-Vlan-interface10] quit
4. 端口工作模式详解及配置
Promiscuous模式(混杂模式)-上行
连接上行设备,可与所有Secondary VLAN通信
# 进入上行端口视图
[H3C] interface gigabitethernet 1/0/5# 配置端口在指定VLAN中工作在promiscuous模式
[H3C-GigabitEthernet1/0/5] port private-vlan 10 promiscuous
[H3C-GigabitEthernet1/0/5] quit
Trunk Promiscuous模式 -上行
上行端口需要传输多个Primary VLAN,允许携带VLAN Tag通过
# 进入上行端口视图
[H3C] interface gigabitethernet 1/0/24
# 配置端口在指定VLAN中工作在Trunk Promiscuous模式
[H3C-GigabitEthernet1/0/24] port private-vlan 10 20 trunk promiscuous
[H3C-GigabitEthernet1/0/24] quit
Host模式(主机模式)-下行
连接终端用户,只能与Primary VLAN和同一Secondary VLAN通信
# 进入下行端口视图
[H3C] interface gigabitethernet 1/0/2# 配置端口的链路类型(三者选其一)
[H3C-GigabitEthernet1/0/1] port link-type access/trunk/hybrid# 将端口加入指定VLAN
# Access端口:
[H3C-GigabitEthernet1/0/1] port access vlan 2
# Trunk端口:
[H3C-GigabitEthernet1/0/1] port trunk permit vlan 2 3
# Hybrid端口:
[H3C-GigabitEthernet1/0/1] port hybrid vlan 2 3 untagged# 配置端口工作在host模式
[H3C-GigabitEthernet1/0/2] port private-vlan host
[H3C-GigabitEthernet1/0/2] quit
Trunk Secondary模式
下行端口需要接入多个Secondary VLAN允许指定Secondary VLAN以Tagged方式通过
# 进入下行端口视图
[H3C] interface gigabitethernet 1/0/10
# 配置端口的链路类型
[H3C-GigabitEthernet1/0/10] port link-type trunk
# 将端口加入指定VLAN
[H3C-GigabitEthernet1/0/10] port private-vlan 2 3 trunk secondary
[H3C-GigabitEthernet1/0/10] quit
5. Private VLAN配置过程示例
promiscuous模式
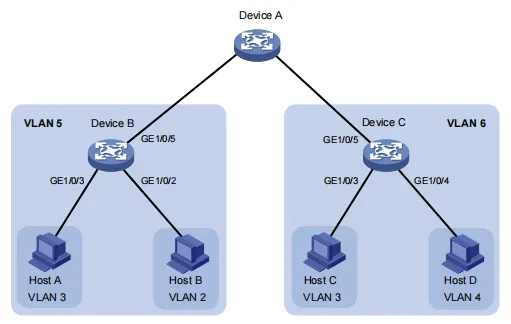
要求:Device B配置Primary VLAN 5,关联Secondary VLAN 2、3,上行端口GigabitEthernet1/0/5工作在promiscuous模式,下行端口分别加入对应Secondary VLAN,工作在host模式。
/*Device B配置*/(配置 Device C类似)
<DeviceB> system-view# 配置 VLAN 5 为 Primary VLAN
[DeviceB] vlan 5
[DeviceB-vlan5] private-vlan primary
[DeviceB-vlan5] quit# 创建Secondary VLAN
[DeviceB] vlan 2 to 3# 建立映射关系
[DeviceB] vlan 5
[DeviceB-vlan5] private-vlan secondary 2 to 3
[DeviceB-vlan5] quit# 配置上行端口
[DeviceB] interface gigabitethernet 1/0/5
# 工作在 promiscuous 模式
[DeviceB-GigabitEthernet1/0/5] port private-vlan 5 promiscuous
[DeviceB-GigabitEthernet1/0/5] quit# 配置下行端口
[DeviceB] interface gigabitethernet 1/0/2
[DeviceB-GigabitEthernet1/0/2] port access vlan 2
# 工作在 host 模式
[DeviceB-GigabitEthernet1/0/2] port private-vlan host
[DeviceB-GigabitEthernet1/0/2] quit[DeviceB] interface gigabitethernet 1/0/3
[DeviceB-GigabitEthernet1/0/3] port access vlan 3
[DeviceB-GigabitEthernet1/0/3] port private-vlan host
[DeviceB-GigabitEthernet1/0/3] quit
Trunk Promiscuous模式
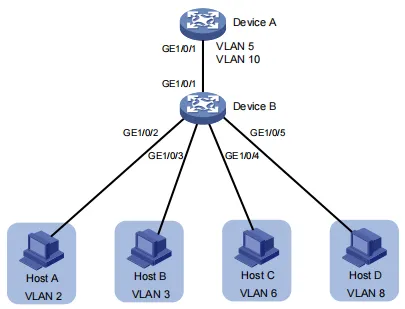
要求:Device B配置多个Primary VLAN(VLAN 5和10),上行端口需要允许多个Primary VLAN以Tagged方式通过。从 Device A 看,下接的 Device B 只有 VLAN 5 和 VLAN 10。
/*Device B配置*/
# 配置Primary VLAN
[DeviceB] vlan 5
[DeviceB-vlan5] private-vlan primary
[DeviceB-vlan5] quit[DeviceB] vlan 10
[DeviceB-vlan10] private-vlan primary
[DeviceB-vlan10] quit# 创建Secondary VLAN
[DeviceB] vlan 2 to 3 6 8# 建立映射关系
[DeviceB] vlan 5
[DeviceB-vlan5] private-vlan secondary 2 to 3
[DeviceB-vlan5] quit[DeviceB] vlan 10
[DeviceB-vlan10] private-vlan secondary 6 8
[DeviceB-vlan10] quit# 配置上行端口为Trunk Promiscuous模式
[DeviceB] interface gigabitethernet 1/0/1
[DeviceB-GigabitEthernet1/0/1] port private-vlan 5 10 trunk promiscuous
[DeviceB-GigabitEthernet1/0/1] quit# 配置下行端口工作在 host 模式
[DeviceB] interface gigabitethernet 1/0/2
[DeviceB-GigabitEthernet1/0/2] port access vlan 2
[DeviceB-GigabitEthernet1/0/2] port private-vlan host
[DeviceB-GigabitEthernet1/0/2] quit[DeviceB] interface gigabitethernet 1/0/3
[DeviceB-GigabitEthernet1/0/3] port access vlan 3
[DeviceB-GigabitEthernet1/0/3] port private-vlan host
[DeviceB-GigabitEthernet1/0/3] quit[DeviceB] interface gigabitethernet 1/0/4
[DeviceB-GigabitEthernet1/0/4] port access vlan 6
[DeviceB-GigabitEthernet1/0/4] port private-vlan host
[DeviceB-GigabitEthernet1/0/4] quit[DeviceB] interface gigabitethernet 1/0/5
[DeviceB-GigabitEthernet1/0/5] port access vlan 8
[DeviceB-GigabitEthernet1/0/5] port private-vlan host
[DeviceB-GigabitEthernet1/0/5] quit
/*Device A配置*/
# 创建 VLAN
[DeviceA] vlan 5 10
# 配置端口为 Hybrid 端口
[DeviceA] interface gigabitethernet 1/0/1
[DeviceA-GigabitEthernet1/0/1] port link-type hybrid
# 允许 VLAN 5 和 VLAN 10 携带 Tag 通过。
[DeviceA-GigabitEthernet1/0/1] port hybrid vlan 5 10 tagged
[DeviceA-GigabitEthernet1/0/1] quit
Secondary VLAN间三层互通配置示例

要求:实现Secondary VLAN间二层隔离、三层互通,通过Primary VLAN接口实现路由功能
/*Device A配置*/
# 配置 Primary VLAN
<DeviceA> system-view
[DeviceA] vlan 10
[DeviceA-vlan10] private-vlan primary
[DeviceA-vlan10] quit
[DeviceA] vlan 20
[DeviceA-vlan20] private-vlan primary
[DeviceA-vlan20] quit
# 创建 Secondary VLAN
[DeviceA] vlan 11 to 12
[DeviceA] vlan 21 to 22# 配置 Primary VLAN 10 和 Secondary VLAN 11、12 的映射关系。
[DeviceA] vlan 10
[DeviceA-vlan10] private-vlan secondary 11 12
[DeviceA-vlan10] quit# 配置 Primary VLAN 20 和 Secondary VLAN 21、22 的映射关系。
[DeviceA] vlan 20
[DeviceA-vlan20] private-vlan secondary 21 22
[DeviceA-vlan20] quit# 配置上行端口 GE1/0/5 在 VLAN 10、 20 中工作在 trunk promiscuous 模式。
[DeviceA] interface gigabitethernet 1/0/5
[DeviceA-GigabitEthernet1/0/5] port private-vlan 10 20 trunk promiscuous
[DeviceA-GigabitEthernet1/0/5] quit# 将下行端口 GE1/0/1 加入 VLAN 22,工作在 host 模式。
[DeviceA] interface gigabitethernet 1/0/1
[DeviceA-GigabitEthernet1/0/1] port access vlan 22
[DeviceA-GigabitEthernet1/0/1] port private-vlan host
[DeviceA-GigabitEthernet1/0/1] quit# 将下行端口 GE1/0/3 加入 VLAN 12,工作在 host 模式。
[DeviceA] interface gigabitethernet 1/0/3
[DeviceA-GigabitEthernet1/0/3] port access vlan 12
[DeviceA-GigabitEthernet1/0/3] port private-vlan host
[DeviceA-GigabitEthernet1/0/3] quit# 配置下行端口 GE1/0/2 在 VLAN 11 、21 中工作在 trunk secondary 模式。
[DeviceA] interface gigabitethernet 1/0/2
[DeviceA-GigabitEthernet1/0/2] port private-vlan 11 21 trunk secondary
[DeviceA-GigabitEthernet1/0/2] quit
6. 配置验证命令
# 查看Private VLAN配置
display private-vlan
# 查看VLAN信息
display vlan# 查看接口状态
display interface brief
# 查看MAC地址表
display mac-address
以promiscuous模式示例为例:
[DeviceB] display private-vlan
Primary VLAN ID: 5
Secondary VLAN ID: 2-3VLAN ID: 5
VLAN type: Static
Private VLAN type: Primary
Route interface: Not configured
Description: VLAN 0005
Name: VLAN 0005
Tagged ports: None
Untagged ports:GigabitEthernet1/0/2GigabitEthernet1/0/3GigabitEthernet1/0/5VLAN ID: 2
VLAN type: Static
Private VLAN type: Secondary
Route interface: Not configured
Description: VLAN 0002
Name: VLAN 0002
Tagged ports: None
Untagged ports:GigabitEthernet1/0/2GigabitEthernet1/0/5VLAN ID: 3
VLAN type: Static
Private VLAN type: Secondary
Route interface: Not configured
Description: VLAN 0003
Name: VLAN 0003
Tagged Ports: None
Untagged Ports:GigabitEthernet1/0/3GigabitEthernet1/0/5
可以看到,工作在 promiscuous 模式的端口 GE1/0/5 和工作在 host 模式的端口GE1/0/2 和 GE1/0/3 均以 Untagged 方式允许 VLAN 报文通过。
